How to Use Trezor Securely
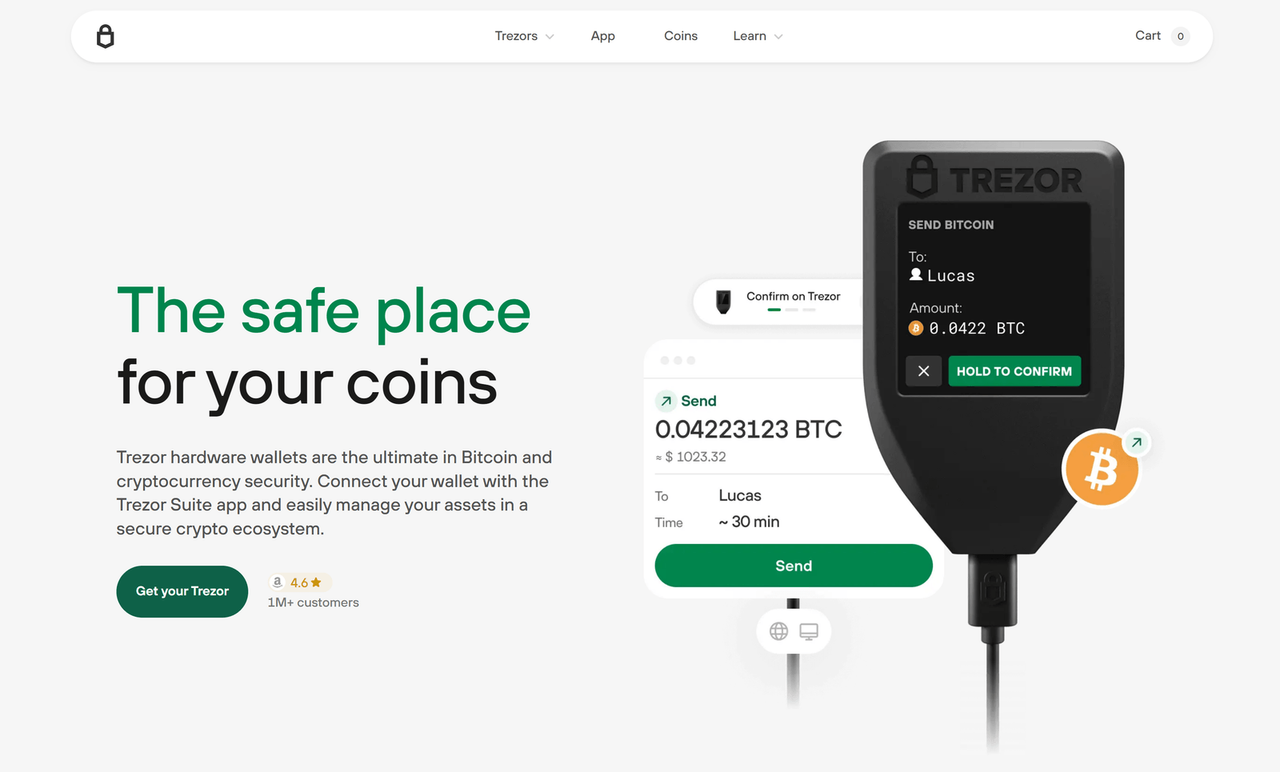
Learning how to use Trezor securely is crucial for anyone serious about protecting their cryptocurrency assets. Whether you are new to crypto or a seasoned investor, understanding the best practices on how to use Trezor securely ensures your private keys remain safe and your transactions stay protected from potential threats.
Trezor Suite: Features You Should Know
To maximize security, exploring Trezor Suite: Features You Should Know is essential. Trezor Suite provides a unified platform for managing your digital assets, and knowing Trezor Suite: Features You Should Know helps you leverage tools like portfolio tracking, transaction history, and firmware updates efficiently.
- Trezor Suite: Features You Should Know include real-time portfolio monitoring for multiple cryptocurrencies, ensuring you always have an overview of your holdings.
- Trezor Suite: Features You Should Know also include secure firmware updates, which are vital to maintaining a safe environment for your private keys.
- Another key Trezor Suite: Feature You Should Know is the integrated exchange interface, allowing you to swap coins without leaving the Trezor Suite platform.
Trezor Suite vs Other Crypto Interfaces
When comparing Trezor Suite vs Other Crypto Interfaces, it's clear that Trezor prioritizes security and user experience. Trezor Suite vs Other Crypto Interfaces highlights advantages such as seamless device connectivity, robust encryption, and a clear interface that reduces the risk of errors.
- Trezor Suite vs Other Crypto Interfaces shows how Trezor Suite provides superior firmware protection, which other wallets may not prioritize as heavily.
- In Trezor Suite vs Other Crypto Interfaces, Trezor Suite’s recovery seed management stands out as a secure and user-friendly solution.
- Trezor Suite vs Other Crypto Interfaces emphasizes the importance of ongoing updates and community support, keeping your crypto management safe and efficient.
How to Use Trezor Securely: Setting Up Your Device
The first step in how to use Trezor securely is proper device setup. Always initialize your Trezor device directly with Trezor Suite and avoid third-party software during setup. Following these steps when learning how to use Trezor securely ensures your device generates a private key in a secure environment.
How to Use Trezor Securely: Protecting Your Recovery Seed
A critical aspect of how to use Trezor securely is safeguarding your recovery seed. Never store it digitally or online, as cybercriminals can exploit unsecured storage. Understanding how to use Trezor securely includes keeping your recovery seed offline and in a safe location, like a fireproof safe or a dedicated security device.
Trezor Suite: Features You Should Know for Daily Transactions
When performing transactions, reviewing Trezor Suite: Features You Should Know for Daily Transactions can significantly improve efficiency and safety. Features like multi-signature support, transaction previews, and fiat value tracking are part of Trezor Suite: Features You Should Know to manage crypto without compromising security.
Trezor Suite vs Other Crypto Interfaces: Why Security Matters
Considering Trezor Suite vs Other Crypto Interfaces, security should always be a top priority. While other interfaces may offer convenience, Trezor Suite vs Other Crypto Interfaces demonstrates that Trezor Suite balances usability with advanced security measures such as PIN protection, passphrase support, and device authentication.
- Trezor Suite vs Other Crypto Interfaces highlights end-to-end encryption that protects your transaction data from third-party interception.
- Understanding Trezor Suite vs Other Crypto Interfaces ensures you select a wallet that regularly updates security protocols to combat emerging threats.
- Trezor Suite vs Other Crypto Interfaces underscores the importance of hardware-based storage compared to purely software wallets.
How to Use Trezor Securely: Best Practices
Adhering to best practices is essential in how to use Trezor securely. Always keep your device firmware updated, verify transaction addresses on the Trezor screen, and avoid connecting your device to public or untrusted networks. These habits form the foundation of how to use Trezor securely and help mitigate risks associated with cryptocurrency theft.
Conclusion: Trezor Suite vs Other Crypto Interfaces and Secure Use
In summary, understanding Trezor Suite vs Other Crypto Interfaces and how to use Trezor securely empowers users to make informed decisions about cryptocurrency storage and transactions. Leveraging the features of Trezor Suite while following secure practices ensures your digital assets remain protected against evolving threats.